Purpose
The goal of this guide is to provide a process and easy steps to follow to ensure your Oracle Cloud Infrastructure (OCI) tenancy is configured to have a high security posture and it is aligned with cloud security best practices as provided by the Center for Internet Security (CIS) OCI Foundations Benchmark and Oracle. Regardless of whether you’re starting with a fresh OCI Tenancy or managing one with existing workloads, the objective remains consistent: to assure the security of your tenancy and maintain that security over time.
In this blog we will focus on highly recommended security controls and will address additional recommended security controls in a subsequent blog post.
Throughout the blog we will reference our Security Guide Github repo that hosts a wealth of links to blogs, integration guides and Oracle documentation.
If you are looking for prescribed guidance on setting up foundational security in a new tenancy or assessing the security posture of your existing tenancy, skip ahead by use the links below.
- OCI Tenancy Security Best Practices Guide – New tenancy
- OCI Tenancy Security Best Practices Guide – Existing tenancy
Concepts
Before diving into recommendations, we need to introduce a few concepts and industry standards.
Center for Internet Security
Oracle and cyber security experts across the industry have collaborated with the Center for Internet Security (CIS) to publish prescriptive guidelines outlining the recommended deployment practices within Oracle Cloud Infrastructure. These practices include the configuration of various controls to maintain a robust security posture.
Oracle Best Practices
As cloud security and network solution architects, we have been working to help customers implement security controls since OCI was first launched. Over the years we have identified multiple customer pain points and design challenges. Our organization’s recommendations and best practices are collectively referred as the “Oracle Best Practices”.
CIS OCI Benchmark
Most of our best practices and recommendations on Tenancy design are anchored around the Center for Internet Security (CIS) OCI Foundations Benchmark and recommendations it provides.
If you are using a different security framework, you can follow this documentation to see how you can map CIS security controls and other frameworks such as NIST, ISO, HIPAA, PCI, SOC 2.
CIS OCI Landing Zone
The CIS OCI Landing Zone architecture facilitates the automated deployment of a secure OCI tenancy that aligns to the CIS Foundations Benchmark recommendations. In addition, the Terraform based Landing Zone provisions resources needed to support meeting the highly recommended controls that we detail further below in this document. The Terraform template is publicly available in GitHub under the oracle-quickstart project. The quickstart can be used as-is or be customized if desired. If you have any questions or issues, please file an issue in the Landing Zone’s GitHub repository.
CIS Compliance Checker
Oracle has created an assessment script that can be run against any OCI tenancy to evaluate the compliance with the CIS OCI Foundations Benchmark and Oracle Best Practices. The script provides insights into areas that are not compliant with the benchmark along with recommendations on how to remediate them.
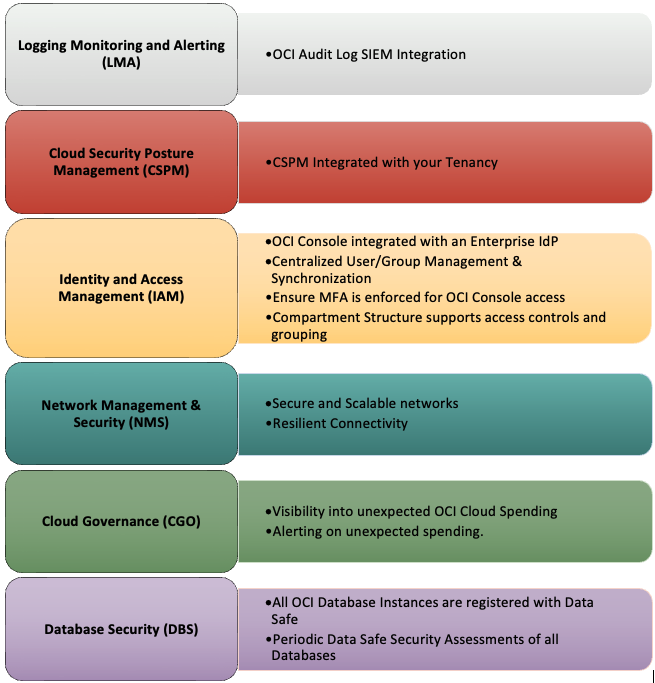
Security Recommendations
To strengthen the security posture of their OCI tenancy we recommend focusing on six foundational security control areas.
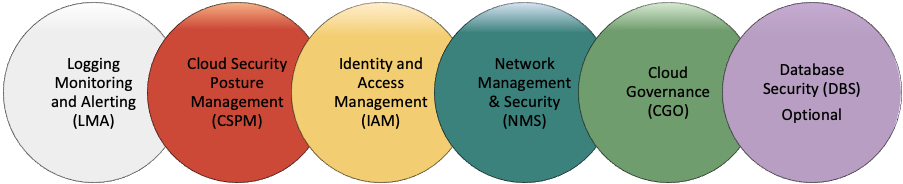
Logging, Monitoring and Alerting
The ability to proactively have logs on Security related events presented for triage to the relevant resources is key to the detection and prevention of Cyber Security Incidents. Many organizations utilize Security Information and Event Management (SIEM) platforms to correlate and analyze logs and alerts from relevant assets.
Highly recommended Controls:
- OCI Audit Log SIEM Integration
Send tenancy-wide audit logs from all regions to a SIEM for forensic, alerting, and analytical purposes.
Cloud Security Posture Management
Visibility into your tenancy’s security posture by continuous scanning and alerting on deviation from defined security baselines is critical. This can prevent misconfiguration and drift that could expose attack vectors.
Highly recommended Controls:
- CSPM Integrated with your Tenancy
Use native CSPM capabilities or third-party tools to scan the tenancy and alert on findings.
Identity and Access Management
Enforcing a unified way of authentication to the OCI Console via an Enterprise Identity Provider and enforcing security controls like Multi-Factor Authentication (MFA) for all users is a key component along with centrally managed user lifecycle. Access to resources should be governed by a separation of duties approach, allowing users access only to resources needed to perform their job role.
Highly recommended Controls:
- OCI Console integrated with an Enterprise Identity Provider (IdP) for Single Sign-On (SSO)
Ensure enterprise SSO credentials are used access the OCI Console instead of managing additional credentials.
- Centralized User/Group Lifecycle Management
To ensure good account hygiene and reduce the risk of human error when performing user management. When utilizing an IdP configured with System for Cross-Domain Identity Management (SCIM) protocol, you can securely automate the exchange of user identity data throughout the user provisioning lifecycle. For example, if a new hire joins the company, the new user is automatically provisioned, or if an employee is terminated, access is revoked.
- Ensure Multi-Factor Authentication is enforced for any OCI Console access
A key CIS recommendation that adds an extra layer of security during the login process making it harder for unauthorized users to gain access to OCI resources.
- Compartment structure supports access controls and grouping
Ensure the compartment structure supports logical grouping of resources that align with the operating model of your teams and allows for efficient scaling of access controls when adding workloads.
Network Management and Security
The implementation of a secure and scalable network architecture is as critical in Cloud based environments as in the traditional on-premises deployments. It is important that the topology provides traffic inspection and resilient connectivity as needed without requiring major architectural updates.
Highly recommended Controls:
- Secure and Scalable networks
Ensure a secure and scalable architecture for current and foreseeable future workload(s) is in place. Hub and Spoke topologies are a common way to meet this requirement as you can inspect traffic via the hub Virtual Cloud Network (VCN). We recommend utilizing technologies such as a network security groups, and network firewalls to inspect and restrict ingress and egress traffic. Other best practices include having dedicated compartments and VCNs for Dev/Test, Non-Prod, and Production workloads. - Resilient Connectivity
Ensure the diversity and resiliency of OCI connectivity to on-premises and other clouds are aligned with your company requirements. Ensure there are no single points of failure, and that you have conducted a full test of failing-over/failing-back.
Cloud Governance
The focus in this domain is around visibility into cloud spending and provisioned assets in a tenancy. Especially having tooling and processes in place to quickly detect any unexpected spending either due to a compromise or unsanctioned resource creation.
Highly recommended Controls:
- Visibility into unexpected OCI cloud spending
Ensure you have visibility into cloud spending, especially unexpected spending. - Alerting on unexpected spending
Ensure the right people are notified of unexpected costs.
Database Security
Database Security controls are essential as they protect the data where it resides, mitigating or preventing damage to the availability, integrity and/or confidentiality of the data. Processes and tooling should be in place to continuously scan database in the tenancy and report deviations from security baseline configurations.
Highly recommended Controls:
- All OCI Database Instances are registered with Data Safe
Leverage native Data Safe Service capabilities to monitor and assess the security profile and compliance of all OCI databases. - Periodic Data Safe Security Assessments of all Databases
Ensure Security assessments for all registered databases run at least every 90 days.
Summary of highly recommended security controls:
Where are you on your OCI tenancy journey?
Understanding your current OCI Tenancy security posture and configured settings is crucial, as it will influence the approach you should adopt.
We typically see two types of scenarios:
- A new tenancy with no or a few resources provisioned and no workloads running.
- An existing and established tenancy with production workloads running.
The approach for a new tenancy, is mostly straight forward since we know the current state and don’t need to factor in running production workloads.
Despite the unique configurations of an existing tenancy, conducting an assessment to gauge alignment with our highly recommended security controls remains straightforward. Following this assessment, defining the approach and potential remediation tasks, along with their risk assessment, planning, and execution, becomes manageable.
Next steps
So far, we’ve provided an overview of concepts, security domains and controls within those domains that we highly recommend you review.
The next step in securing your tenancy is to select one of our specific blogs covering either the new tenancy or existing tenancy scenarios in a lot more detail.
- OCI Tenancy Security Best Practices Guide – New tenancy
- OCI Tenancy Security Best Practices Guide – Existing tenancy
Additional recommended resources
- We suggest to review the Best Practices Framework for Oracle Cloud Infrastructure solution playbook as it provides a broader overview of the key items that should be on any customer’s project plan to deploy their first workload on OCI or to check their existing tenancy to ensure that they are leaning on the experiences gained by other Oracle customers.
- Watch our “Deploying Oracle Cloud Infrastructure Center for Internet Security Landing Zone” workshop.
- Review our solution playbook about incorporating Cyber-Resilience capabilities into your OCI tenancy.